News 2015
Model-based security in Embedded Systems

The ubiquitous presence of networked embedded devices comes as no surprise.
Large computing infrastructures that bring automation in our daily lives exist
due to support of such devices interconnected through networks. Being a part of
such infrastructures, embedded devices carry and process sensitive information.
Thus, both their exposure to open networks and their critical role in storing,
processing, and transmission of information makes embedded devices a target of
sophisticated attacks. The interest of attackers is stimulated by the fact that
modern embedded systems are often easily accessible (e.g. deployed in a public
and untrusted environment) and the consequences of compromising such devices
can be very large. These facts impose high requirements on security standards
for embedded systems that are often neglected.
It goes without saying that security issues should be considered during
embedded system development since insufficient security can create a
substantial risk for society and significant loss of profits for embedded
system producers, owners, and end users. In these realities the task of
assuring security properties of embedded systems becomes more challenging which
immediately leads to an emergent need in specific methods and tools to support
the development of embedded systems.
In a recent PhD thesis at IDA, Maria Vasilevskaya proposes a Security-Enhanced
Embedded system Design (SEED) approach, which is a set of concepts, methods,
and processes that together aim at addressing this challenge by bridging the
gap between the two areas of expertise, i.e. security experts and embedded
system engineers.
Read more
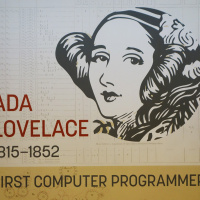
Celebrating Ada Lovelace 200 years
A celebration of 200 years from Ada Augusta Lovelace's birthday took place with
a lively program and presentation of a large wallpaper image on a central wall
near the conference room Visionen. This places the role of the first programmer
and woman role model on today's agenda.
Read more
Mattias Tiger winner of SAIS Master Thesis Award 2015
Mattias Tiger, now a PhD student at IDA, is the winner of the Swedish AI
Society's prize for best AI Master Thesis 2015. The title of the thesis is
"Unsupervised Spatio-Temporal Activity Learning and Recognition in a Stream
Processing Framework". The project was supervised by Daniel de Leng and Fredrik
Heintz.
Read more
2015 Wilkes Stipendium award
The third awarding of Wilkes stipendium, a prize given to a female computer
science/engineering or IT student that has a distinguishing record has taken
place with Hanna Sterneling as the award winner. Hanna studies in the second
year of the Information Technology engineering program. The 2015 prize was
awarded in the IDA Autumn lunch meeting.
Read more
Thermal Issues in Testing of Advanced Systems on Chip
Many cutting-edge computer and electronic products are powered by advanced
Systems-on-Chip (SoC). Advanced SoCs encompass superb performance together with
large number of functions. This is achieved by efficient integration of huge
number of transistors. Such very large scale integration is enabled by a
core-based design paradigm as well as deep-submicron and 3D-stacked-IC
technologies. These technologies are susceptible to reliability and testing
complications caused by thermal issues. Three crucial thermal issues related to
temperature variations, temperature gradients, and temperature cycling are
addressed in Nima Aghaee's PhD thesis.
All the proposed techniques have been implemented and evaluated with extensive
experiments based on ITC'02 benchmarks as well as a number of 3D stacked ICs.
Experiments show that the proposed techniques work effectively and reduce the
costs, in particular the costs related to addressing thermal issues and
early-life failures. Experiments demonstrate that a proposed fast temperature
simulation technique reduces the schedule generation time by more than half.
Read more
Efficient Troubleshooting of Trucks
Trucks and buses are vehicles that primarily are used in commercial operation.
When a fault occurs on such a vehicle it is important that it is repaired as
quickly and cost-efficiently as possible. Modern vehicles are complex and
consists of several interacting mechanical, hydraulic, and electronic systems.
This can make it difficult for a mechanic to troubleshoot the vehicle when the
fault is unknown.
Håkan Warnquist's PhD-thesis in computer science, "Troubleshooting Trucks -
Automated Planning and Diagnosis", describes methods for computing which
actions need to be done in order to troubleshoot and repair a vehicle as
cost-efficiently as possible. In the thesis it is described how to compute the
probabilities of a certain fault given that which can be observed or measured.
New algorithms have been developed for computing which actions need to be done
in order to minimize the cost regarding labor, downtime, and consumed
resources. These techniques can for example be used in software tools to
support the mechanic with information about which faults the vehicle may have
and how to best proceed with the troubleshooting. With such computer support
the precision of the troubleshooting can be increased and the costs for both
the vehicle owner and the workshop can be reduced.
This research has been conducted together with the vehicle manufacturer Scania
under supervision by Prof. Patrick Doherty and Dr. Jonas Kvarnström at the
Department of Computer and Information Science at Linköping University.
Financed by Scania and Vinnova through the programs Vehicle-ICT and FFI
Transport Efficiency.
Read more
RICS research centre kicks off

A five year research project to start up a centre on Resilient Information and
Control Systems (RICS) has been granted SEK 20 million financing from the
Swedish Civil Contingencies Agency (MSB). The centre will be led by Simin
Nadjm-Tehrani and collaborates with researchers from KTH and Chalmers.
Relying on service continuity for societal functions starts by understanding
the complex socio-technical systems that must operate to e.g. deliver
electricity, water, heat and other critical services to society. RICS will help
to understand the risks and vulnerabilities in the information and
communication (ICT) infrastructure on which these services rely. It will then
help to improve their security by providing methods for prevention of attacks
and failures, as well as monitoring and detecting ongoing adverse events.
RICS will increase the competence in the area of ICT security for critical
infrastructure by world class research, and an increased emphasis on these
topics within undergraduate and graduate education. The research topics are
based on three pillars:
* Data analysis and emulation
* Risk and vulnerability analysis using attack modelling
* Real-time detection of adverse events and anomalies
Read more
Timing Analysis of Distributed Embedded Systems

Today's distributed embedded systems are exposed to large variations in
workload due to complex software applications and sophisticated hardware
platforms. Examples of such systems are automotive and avionics applications.
The tasks running on computational units have variable execution times. Thus,
the workload that the computational units must accommodate is likely to be
stochastic. Some of the tasks trigger messages that will be transmitted over
communication buses. There is a direct connection between the variable
execution times of the tasks and the moments of triggering of these messages.
Thus, the workload imposed on the communication buses will also be stochastic.
The likelihood for transient faults to occur is another dimension for
stochastic workload as today's embedded systems are designed to work in extreme
environmental conditions.
Given the above, the need for tools that can analyze systems that experience
stochastic workload is continuously increasing. In a recent PhD theses at IDA,
Bogdan Tanasa addresses this need. The solutions proposed in the thesis have
been validated by extensive experiments that demonstrate the efficiency of the
presented techniques.
Read more
Best Student Paper Award at RTAS 2015
Amir Aminifar has got the Best Student Paper Award at the 21st IEEE Real-Time
and Embedded Technology and Applications Symposium (RTAS), that has been held
in Seattle, USA. RTAS is a major event, highly selective, and among the most
prestigious in the area.
Amir's paper addresses one of the most interesting issues in the context of
modern cyber-physical systems, namely how to bridge the gap between the control
theoretical and the computer engineering view of designing efficient control
systems. Proposing a solution that globally captures the control theoretical
and real-time scheduling aspect, this work is a step towards resource efficient
implementations of high quality and safe control applications.
Read more
On combinatorial optimization
Some optimization problems are practically unsolvable; the algorithms we have
at disposal have enormous running times. Other problems, however, can be solved
efficiently.
Why is it like this? What properties is it that make problems easy to solve, or
conversely, difficult to solve? Questions of this type are studied by Hannes
Uppman in a recent PhD thesis at IDA about the complexity of combinatorial
optimization problems.
Read more
D40IT20 jubileum conference
Among the speakers at the D40IT20 jubileum conference there were several alumni
including John Wilander at Apple who travelled from Cupertino, Helena Mischel
from Microsoft, Ulrik Lindblad from SP devices and Petter Weiderholm from
Spotify. There were also presentations by Prof. Tracy Hammond from Texas A&M
University with interests in AI, haptics and situational awareness, and concept
learning, as well as Erik Kruse, marketing strategist from Ericsson who gave an
impression of tomorrow's connected world.
The program was completed with entertainment, cake, and mingle among students,
alumni, and faculty members.
Read more
Best student Thesis award
The annual prize for Master and Bachelor level theses was awarded in the context of the Jubileum celebration of D40-IT20 with LiU alumni and students from D, IT, and U five year programs. The wining candidates, among five nominated were Viktor Löfgren and Klervie Toszé.
Page responsible: Webmaster