
Mohammad Borhani
PhD student
About me
I received an M.Sc. degree in Software Engineering from Mälardalen University, Sweden, where I completed an industrial master's thesis with ABB in Västerås. I was an Erasmus+ International Credit Mobility (ICM) student at Mälardalen University. I also hold an M.Sc. degree in Computer Engineering from the School of Electrical and Computer Engineering, University of Tehran, where I graduated with an A-level MSc score. Additionally, I was the top graduate in my B.Sc. program. Currently, I am a fourth-year Ph.D. student at Linköping University in the Department of Computer and Information Science. My main research interests include VPN, SDN, network security, and communication network optimization.
Research
- Communication Networks
- Network Optimization
- VPLS
- SDN
- Host Identity Protocol (HIP)
Education
- MSc in Computer Science, 2021
- Mälardalens University, (Industrial Thesis with ABB Sweden)
- Msc In Computer Engineering, 2020
- University of Tehran, Iran
Recent Publications
Towards Secure and Scalable Provider-Provisioned Layer 2 VPNs: Embracing Zero Trust Approach -- IEEE Transactions on Consumer Electronics-2026
A sharp increase in cyberattacks targeting industrial systems highlights the need for remote connectivity that remains secure even as deployments scale across many sites. While Virtual Private LAN Service (VPLS) offers efficient and logically isolated Layer 2 VPNs for industrial and enterprise deployments, current solutions operate under the assumption that customer sites fully trust the provider infrastructure to enforce security. This trust model creates a single point of failure, placing the security and privacy of customer networks at risk in the event of provider-side breaches, misconfigurations, or malicious activity. This paper introduces a scalable, Zero Trust architecture for Layer 2 Provider-Provisioned VPNs (PPVPNs) that eliminates the need to trust provider edge (PE) routers. We propose enhancements to the Host Identity Protocol (HIP) through a multiparty key agreement mechanism, integrated into a modified HIP base exchange (HIP-MBEX), which enables integrity protection and authentication among participating routers without requiring customers to trust the provider network. Our HIP-MBEX also incorporates mechanisms to detect and eliminate malicious PE routers during group key generation. To address scalability bottlenecks in HIP-based VPLS, we adopt a hub-and-spoke relaying design that minimizes control plane overhead and reduces memory footprint in PE routers. The proposed architecture is evaluated using real-world network topologies and traffic demand matrices from operational networks. Experimental results show that HIP-MBEX scales efficiently, maintaining setup latency below 200 ms for mid-scale deployments, and reaches 1.7 seconds when scaled to large deployments of 100 nodes. Compared to existing secure VPLS solutions, our design reduces control plane signaling overhead from 10.6 MB to 26 KB at 100 nodes. Additionally, the use of group-based security associations lowers per-packet cryptographic costs and memory footprint at PE routers. On the data plane, HIP-MBEX keeps latency close to the IP baseline and reduces end-to-end latency by 8.3% on average compared to current HIP-based solutions.
PDF
Secure Scalable VPLS: A Lagrangian Relaxation Approach to Tunnel Relaying Optimization -- IEEE Transactions on Networking-2025
Virtual Private LAN Service (VPLS) is commonly used for secure multi-point communication across geographically scattered industrial sites, simulating a unified LAN broadcast domain for Industrial IoT (IIoT)-type devices. This configuration demands a fully-connected overlay network with encrypted Host Identity Protocol (HIP)/IPsec tunnels exhibiting quadratic scalability to the number of tunnels and a significant increase in forwarding table entries. Herein, we introduce Tunnel Relay Nodes (TRNs) as selected routers that maintain full-mesh connectivity. This approach allows non-TRN routers, or Provider Equipment (PEs) acting as spoke PEs, to connect via a TRN. We explore the challenges of using TRNs in secure HIP-based VPLS (HIPLS) networks, including (i) placing reliable TRNs within provider networks and (ii) scheduling TRNs to minimize their activation/deactivation costs as well as the connection cost among PEs. We then demonstrate how (i) can be addressed in polynomial time using a modified general median problem approach. Additionally, we formulate (ii) as a Mixed Integer Linear Programming (MILP) scheduling problem and prove its NP-completeness. Furthermore, we introduce an algorithm based on Lagrangian relaxation to address the intractability in large-scale deployments. This algorithm offers fast, near-optimal solutions while simultaneously balancing solution quality and execution time. Our simulations on three real-world network topologies with real network demands show a 92% average reduction in forwarding table entries on PE. Compared to existing solutions, our method reduces the number of tunnels established by up to 95%, at the expense of a 1.39-fold increase in tunnel path length.
PDF
A critical analysis of the industrial device scanners’ potentials, risks, and preventives -- Journal of Industrial Information Integration-2024
Industrial device scanners allow anyone to scan devices on private networks and the Internet. They were intended as network security tools, but they are commonly exploited as attack tools, as scanning can reveal vulnerable devices. However, from a defensive perspective, this vulnerability disclosure could be used to secure devices if characteristics such as type, model, manufacturer, and firmware could be identified. Automated scanning reports can help to apply security measures before an attacker finds a vulnerability. A complete device recognition procedure can then be seen as the basis for auditing networks and identifying vulnerabilities to mitigate cyber-attacks, especially among Industrial Internet of Things (IIoT) devices that are part of critical systems. In this survey, considering SCADA (Supervisory Control and Data Acquisition) systems as monitoring and control components of essential infrastructure, we focus on analyzing the architectures, specifications, and constraints of several industrial device scanners. In addition, we examine the information revealed by the scanners to identify the threats posed by them on industrial systems and networks. We analyze monthly and yearly statistics of cyber-attack incidents to investigate the role of these scanners in accelerating attacks. By presenting the findings of an experimentation, we highlight how easily anyone could identify hundreds of Internet-connected industrial devices in Sweden, which could lead to a major service interruption in industrial environments designed for minimal human involvement. We also discuss several methods to avoid scanners or reduce their identifying capabilities to conceal industrial devices from unauthorized access.
PDF
KDC Placement Problem in Secure VPLS Networks -- IEEE Transactions on Information Forensics and Security-2023
Virtual Private LAN Service (VPLS) is a VPN technology that connects remote client sites with provider networks in a transparent manner. Session key-based HIPLS (S-HIPLS) is a VPLS architecture based on the Host Identity Protocol (HIP) that provides a secure VPLS architecture using a Key Distribution Center (KDC) to implement security mechanisms such as authentication, encryption, etc. It exhibits limited scalability though. Using multiple distributed KDCs would offer numerous advantages including reduced workload per KDC, distributed key storage, and improved scalability, while simultaneously eliminating the single point of failure of S-HIPLS. It would also come with the need for optimally placing KDCs in the provider network. In this work, we formulate the KDC placement (KDCP) problem for a secure VPLS network as an Integer Linear Programming (ILP) problem. The latter is NP-hard, thereby suggesting a high computational cost for obtaining exact solutions especially for large deployments. Therefore, we motivate the use of a primal-dual algorithm to efficiently produce near-optimal solutions. Extensive evaluations on large-scale network topologies, such as the random Internet graph, demonstrate our method’s time-efficiency as well as its improved scalability and usefulness compared to both HIPLS and S-HIPLS.
PDF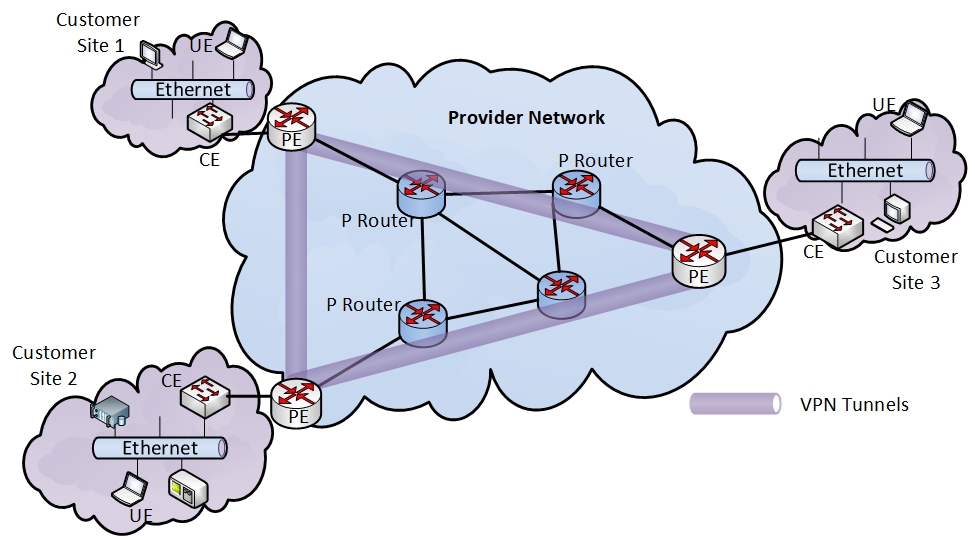
Optimization of Relay Placement for Scalable Virtual Private LAN Services -- FIRA-SIGCOMM-2022
Virtual Private LAN Services are becoming popular for securely connecting geographically dispersed devices to a common protected LAN network isolated from the rest of the Internet. Traditional IP routing protocols cannot provide such connectivity; thus an overlay network of encrypted HIP/IPsec tunnels can be used instead. However, the number of full-mesh tunnels between communicating devices grows exponentially to the number of devices thereby suggesting the investigation of alternatives. The introduction of relaying, which entails selecting a subset of hub routers to retain full-mesh connectivity, allows non-hub routers, the so-called spokes, to maintain connectivity via a hub. In this work, we study the effect of relay-based routing that minimizes the number of hubs, the connection cost between spokes and hubs, the cost of connecting hubs, and the hubs deployment cost. Additionally, we prove that this minimization problem is NP-hard and, thus, intractable for large scale networks. Therefore, we propose an algorithm with provable guarantees that provides an approximate but efficient solution. Initial simulation results indicate a reduction by more than 90% in the memory required for routing tables at the expense of a minor increase in the tunnel path length.
PDF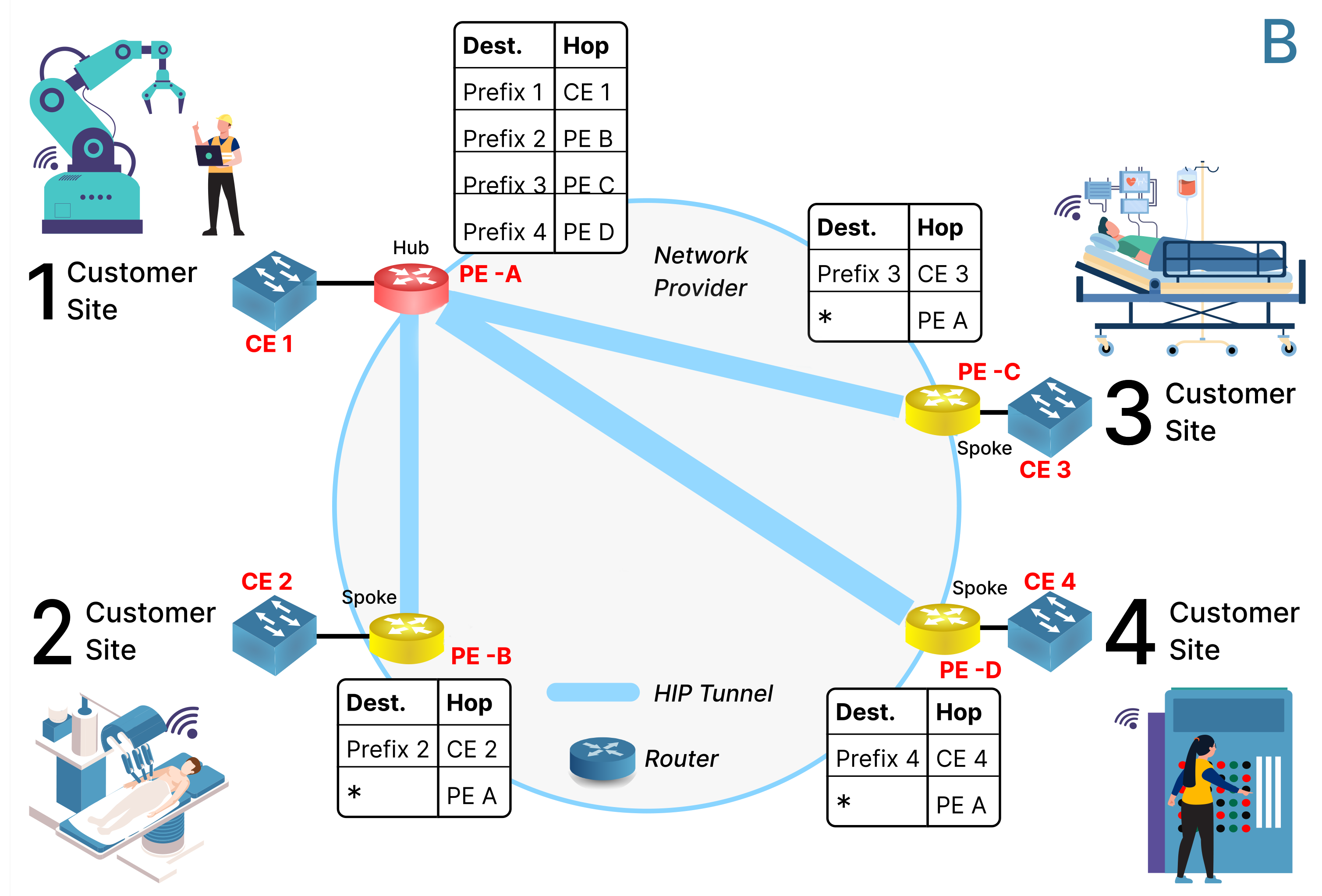
A Survey of Virtual Private LAN Services (VPLS): Past, Present and Future -- Computer Networks-2021
Virtual Private LAN services (VPLS) is a Layer 2 Virtual Private Network (L2VPN) service that has gained immense popularity due to a number of its features, such as protocol independence, multipoint-to-multipoint mesh connectivity, robust security, low operational cost (in terms of optimal resource utilization), and high scalability. In addition to the traditional VPLS architectures, novel VPLS solutions have been designed leveraging new emerging paradigms, such as Software Defined Networking (SDN) and Network Function Virtualization (NFV), to keep up with the increasing demand. These emerging solutions help in enhancing scalability, strengthening security, and optimizing resource utilization. This paper aims to conduct an in-depth survey of various VPLS architectures and highlight different characteristics through insightful comparisons. Moreover, the article discusses numerous technical aspects such as security, scalability, compatibility, tunnel management, operational issues, and complexity, along with the lessons learned. Finally, the paper outlines future research directions related to VPLS. To the best of our knowledge, this paper is the first to furnish a detailed survey of VPLS.
PDF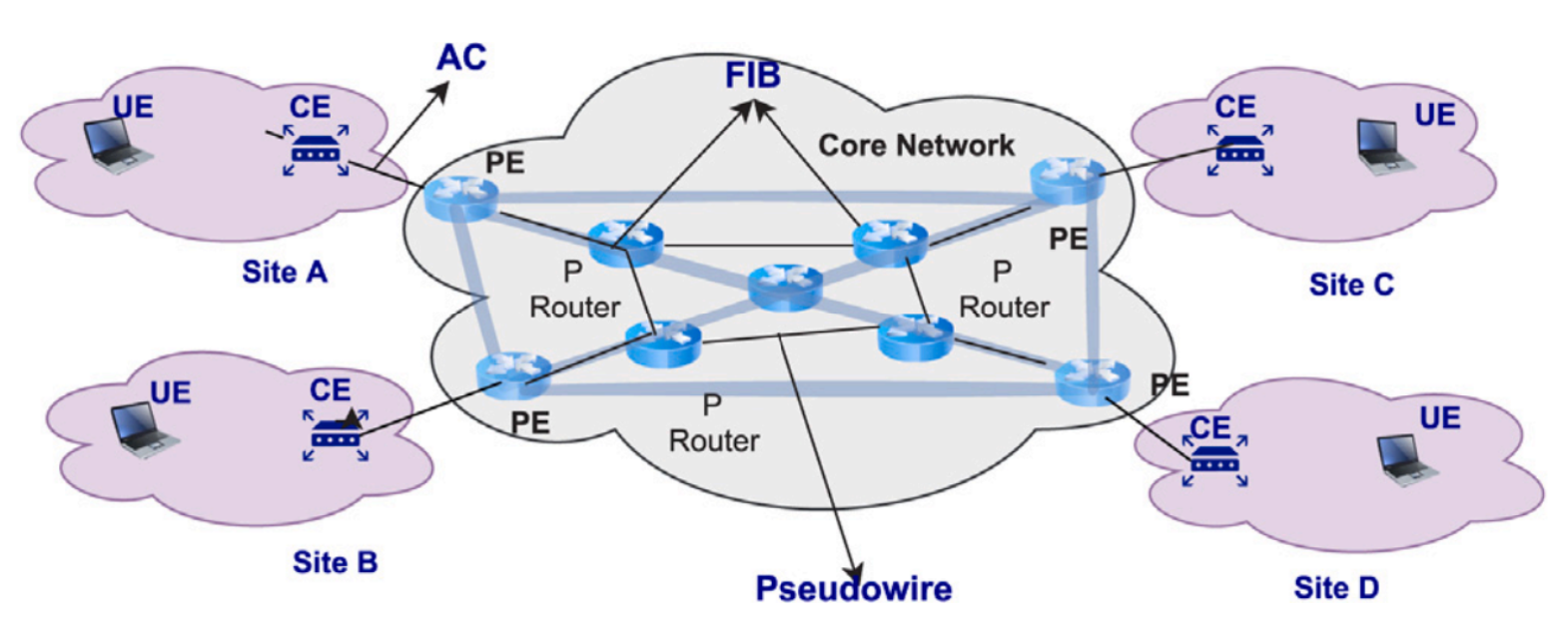
Secure and Resilient Communications in the Industrial Internet -- Book Chapter: Guide to Disaster-Resilient Communication Networks-2020
The Industrial Internet brings the promise of increased efficiency through on-demand manufacturing and maintenance, combining sensors data from engines and industrial devices with big data analysis in the cloud. In this chapter, we survey the main challenges that the Industrial Internet faces from a networking viewpoint. We especially focus on security, as critical industrial components could be exposed over the Internet, affecting resilience. We describe two approaches, Identity-Defined Networking and Software-Defined Virtual Private LAN Services as potential network architectures for the Industrial Internet.
PDF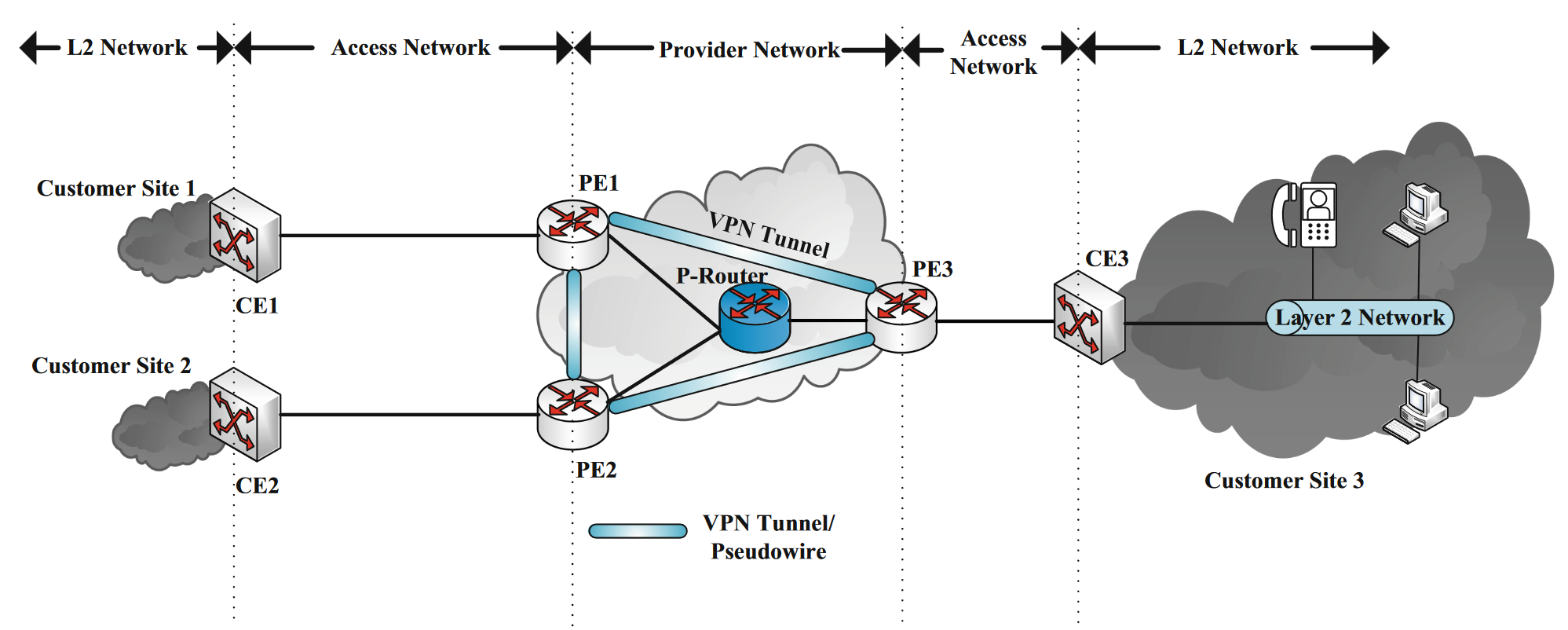
Multi-Armed Bandit Learning for Cache Content Placement in Vehicular Social Networks -- IEEE Communications Letters-2019
In this letter, the efficient dissemination of content in a socially-aware cache-enabled hybrid network using multi-armed bandit learning theory is analyzed. Specifically, an overlay cellular network over a vehicular social network is considered, where commuters request for multimedia content from either the stationary road-side units (RSUs), the base station, or the single mobile cache unit (MCU), if accessible. Firstly, we propose an algorithm to optimally distribute popular contents among the locally deployed RSU caches. To further maximize the cache hits experienced by vehicles, we then present an algorithm to find the best traversal path for the MCU based on commuters' social degree distribution. For performance evaluation, the asymptotic regret upper bounds of the two algorithms are also derived. Simulations reveal that the proposed algorithms outperform existing content placement methods in terms of overall network throughput.
PDF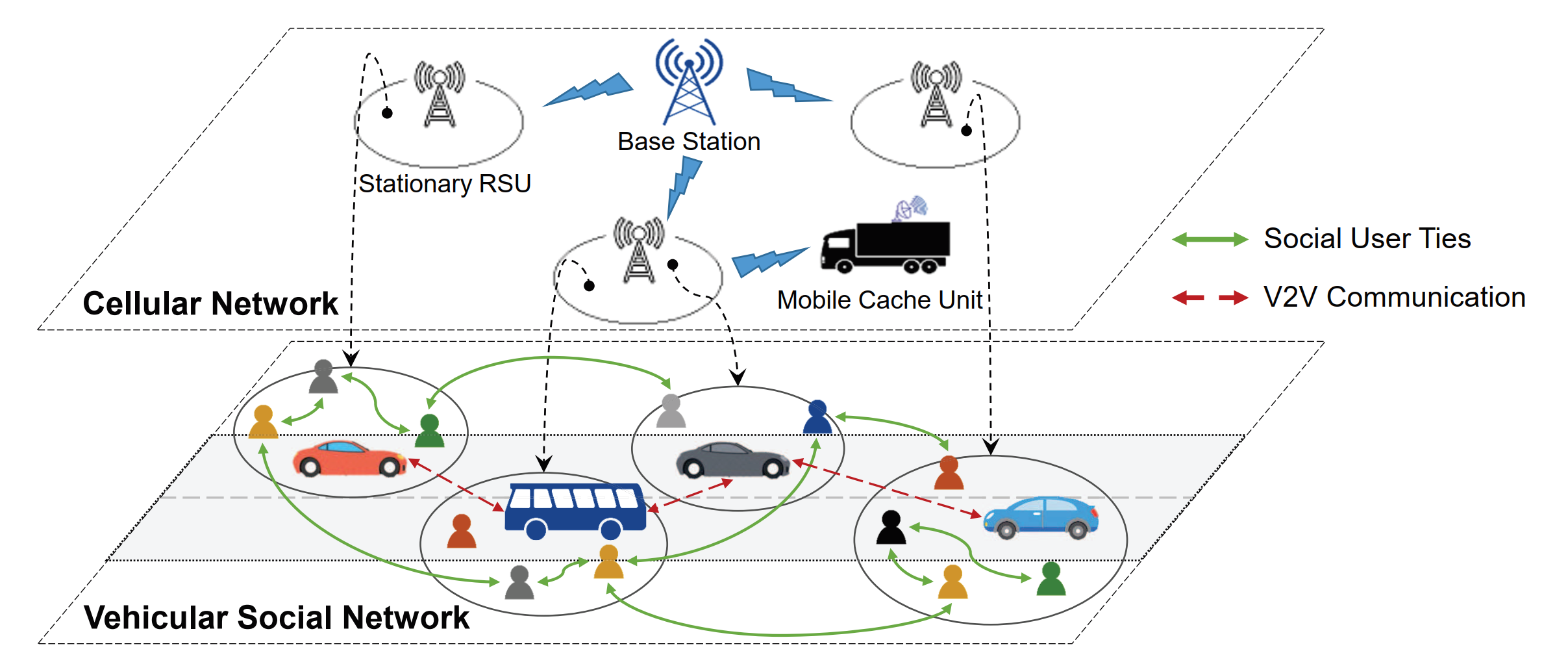
News
- June 2022: Paper acceptance -- FIRA-SIGCOMM2022
- Feb 2023: Paper acceptance -- IEEE Transactions on Information Forensics and Security
- Apr 2024: Paper acceptance -- Journal of Industrial Information Integration
- Jan 2026: Paper acceptance -- IEEE Transactions on Consumer Electronics