Wireshark Lab: IP
|
By Niklas Carlsson and Anna Vapen. Last updated April 2019 by Carl Magnus Bruhner.
(This lab manual is based on "Wireshark Lab: IP", updated to match version 7.0,
by J.F. Kurose, K.W. Ross, available
here.)
|
Contents
Overview of the Assignment
In this lab, we’ll investigate the IP protocol, focusing on the IP datagram. We’ll do so by analyzing a trace of IP datagrams sent and received by an execution of the traceroute program. We’ll investigate the various fields in the IP datagram, and study IP fragmentation in detail.
Before beginning this lab, you’ll probably want to review sections 1.4.3 in the course text book and section 3.4 of RFC 2151 to update yourself on the operation of the traceroute program. You’ll also want to read Section 4.3 in the book, and probably also have RFC 791 on hand as well, for a discussion of the IP protocol.
In this assignment, you will be asked to answer and/or discuss a number of questions. To save time,
it is important that you carefully read the instructions such that you provide answers in the desired format(s).
Capturing packets from an execution of traceroute
In order to generate a trace of IP datagrams for this lab, we’ll use the traceroute program to send datagrams of different sizes towards some destination, X. Recall that
traceroute operates by first sending one or more datagrams with the time-to-live (TTL) field in the IP header set to 1; it then sends a series of one or more datagrams towards the same destination with a TTL value of 2; it then sends a series of datagrams towards the same destination with a TTL value of 3; and so on. Recall that a router must
decrement the TTL in each received datagram by 1 (actually, RFC 791 says that the
router must decrement the TTL by at least one). If the TTL reaches 0, the router returns an ICMP message (type 11 – TTL-exceeded) to the sending host. As a result of this behavior, a datagram with a TTL of 1 (sent by the host executing traceroute) will cause the router one hop away from the sender to send an ICMP TTL-exceeded message back to the sender; the datagram sent with a TTL of 2 will cause the router two hops
away to send an ICMP message back to the sender; the datagram sent with a TTL of 3 will cause the router three hops away to send an ICMP message back to the sender; and
so on. In this manner, the host executing traceroute can learn the identities of the
routers between itself and destination X by looking at the source IP addresses in the
datagrams containing the ICMP TTL-exceeded messages.
We’ll want to run traceroute and have it send datagrams of various lengths.
Note: In this lab you will analyze an already captured trace. However, you are free to capture a live trace from your own computer at home.
Preparing a live trace
-
Windows: The tracert program (used for our ICMP Wireshark lab) provided
with Windows does not allow one to change the size of the ICMP echo request
(ping) message sent by the tracert program. A nicer Windows traceroute
program is pingplotter, available both in free version and shareware versions at
http://www.pingplotter.com. Download and install pingplotter, and test it out by
performing a few traceroutes to your favorite sites. The size of the ICMP echo
request message can be explicitly set in pingplotter by selecting the menu item
Edit -> Options -> Packet Options and then filling in the Packet Size field. The default packet size is 56 bytes. Once pingplotter has sent a series of packets with
the increasing TTL values, it restarts the sending process again with a TTL of 1,
after waiting Trace Interval amount of time. The value of Trace Interval and the
number of intervals can be explicitly set in pingplotter.
-
Linux/Unix/MacOS: With the Unix/MacOS traceroute command, the size of the UDP datagram sent towards the destination can be explicitly set by indicating the number of bytes in the datagram; this value is entered in the traceroute command line immediately after the name or address of the destination. For example, to send traceroute datagrams of 2000 bytes towards gaia.cs.umass.edu, the command would be:
traceroute gaia.cs.umass.edu 2000
Running a live trace at your computer
- Start up Wireshark and begin packet capture (Capture -> Start) and then press OK on the Wireshark Packet Capture Options screen (we’ll not need to select any options here).
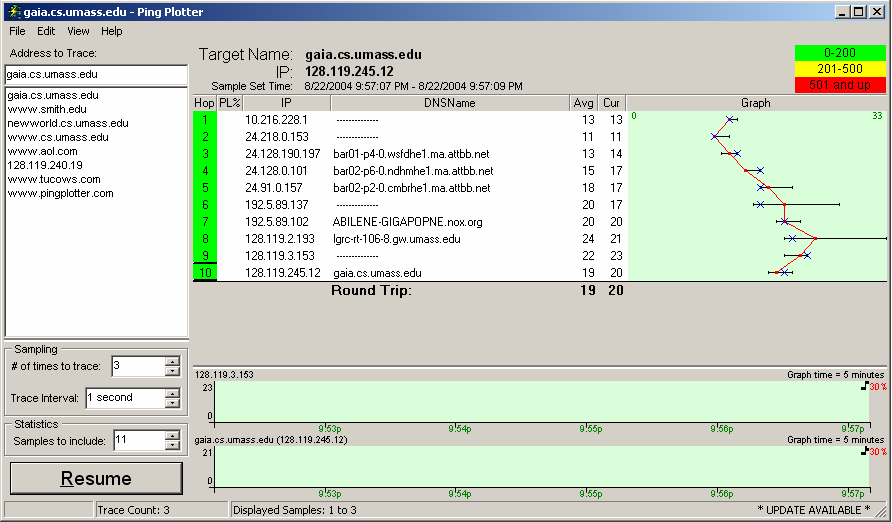
- On Windows at home: If you are using a Windows platform, start up pingplotter and enter the name of a
target destination in the Address to Trace window. Enter 3 in the # of times to Trace field, so you don’t gather too much data. Select the menu item Edit -> Advanced Options -> Packet Options and enter a value of 56 in the Packet Size field and then press OK. Then press the Trace button. You should see a
pingplotter window that looks something like this:
Next, send a set of datagrams with a longer length, by selecting Edit -> Advanced
Options -> Packet Options and enter a value of 2000 in the Packet Size field and then press OK. Then press the Resume button.
Finally, send a set of datagrams with a longer length, by selecting Edit -> Advanced Options -> Packet Options and enter a value of 3500 in the Packet Size field and then press OK. Then press the Resume button.
Stop Wireshark tracing.
- On Linux/Unix/MacOS at home: If you are using a Unix/MacOS platform, enter three traceroute commands, one with
a length of 56 bytes, one with a length of 2000 bytes, and one with a length of 3500 bytes.
Stop Wireshark tracing.
Using an already captured trace
It is recommended to create your own trace, so only use the provided file in case you don't have the option
to create an own trace on a non-school computer.
- At the lab sessions: If you are unable to run Wireshark on a live network connection,
you can download a trace file ipethereal-trace-1
that was captured while following the steps above on one of the author’s Windows computers.
The file is included among the files you downloaded in a previous lab and
can be found here (or
locally).
You may well find it valuable to download this trace even if you’ve captured your own trace and use it,
as well as your own trace, when you explore the questions below.
Analyzing the trace
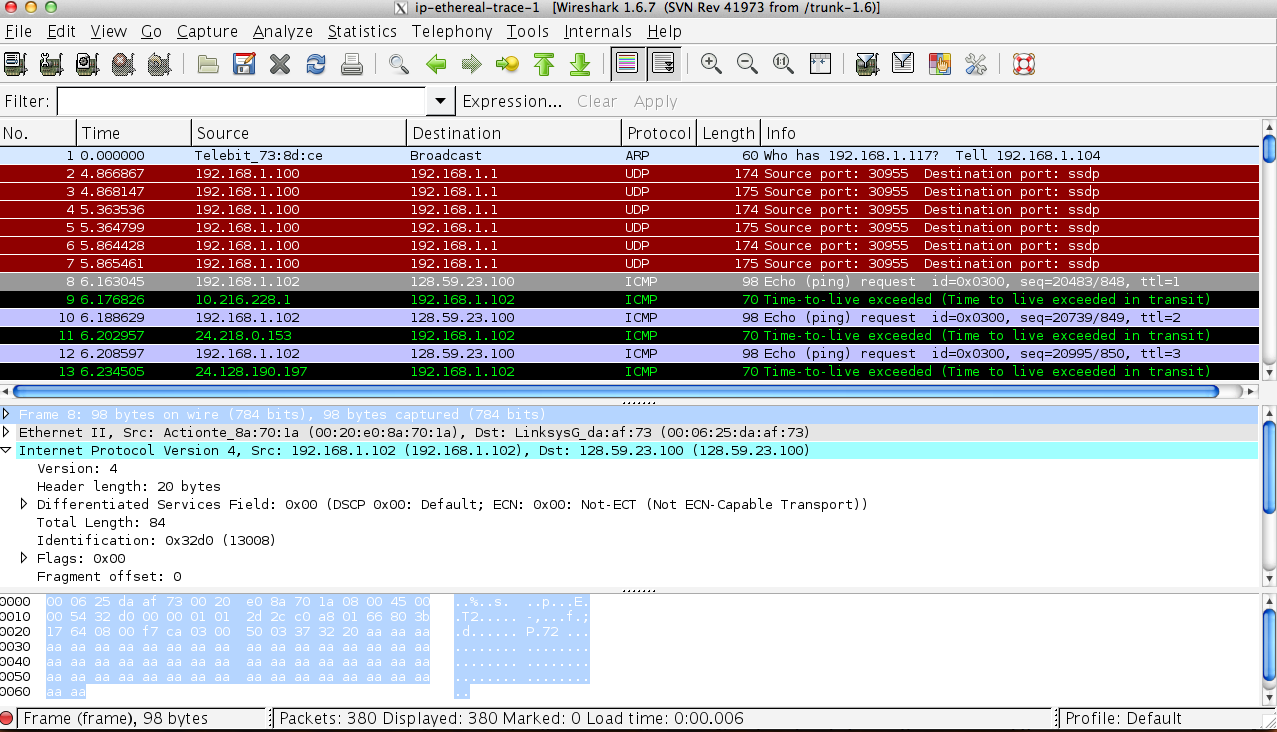
In your trace, you should be able to see the series of ICMP Echo Request (in the case of Windows machine) or the UDP segment (in the case of Unix) sent by your computer and the ICMP TTL-exceeded messages returned to your computer by the intermediate
routers. In the questions below, we’ll assume you are using a Windows machine (or using the already captured trace); the corresponding questions for the case of a Unix machine should be clear.
Whenever possible, when answering a question you should hand in a print screen of the packet(s) within the trace that you used to answer the question asked.
Annotate the printout to explain your answer and support your discussion.
- Select the first ICMP Echo Request message sent by your computer, and expand
the Internet Protocol part of the packet in the packet details window (see figure 2 above).
What is the IP address of your computer?
- Within the IP packet header, what is the value in the upper layer protocol field?
- How many bytes are in the IP header? How many bytes are in the payload of the
IP datagram? Explain how you determined the number of payload bytes.
- Has this IP datagram been fragmented? Explain how you determined whether or
not the datagram has been fragmented.
Next, sort the traced packets according to IP source address by clicking on the Source column header; a small downward pointing arrow should appear next to the word Source.
If the arrow points up, click on the Source column header again. Select the first ICMP
Echo Request message sent by your computer, and expand the Internet Protocol portion
in the Details of selected packet header window. In the Listing of captured packets
window, you should see all of the subsequent ICMP messages (perhaps with additional
interspersed packets sent my other protocols running on your computer) below this first
ICMP. Use the down arrow to move through the ICMP messages sent by your computer.
- Which fields in the IP datagram always change from one datagram to the next
within this series of ICMP messages sent by your computer?
- Which fields stay constant? Which of the fields must stay constant? Which fields
must change? Why?
- Describe the pattern you see in the values in the Identification field of the IP
datagram
Next (with the packets still sorted by source address) find the series of ICMP TTL-exceeded
replies sent to your computer by the nearest (first hop) router.
- What is the value in the Identification field and the TTL field?
- Do these values remain unchanged for all of the ICMP TTL-exceeded replies sent
to your computer by the nearest (first hop) router? Why?
Fragmentation
Sort the packet listing according to time again by clicking on the Time column.
- Find the first ICMP Echo Request message that was sent by your computer after
you changed the Packet Size in pingplotter to be 2000. Has that message been
fragmented across more than one IP datagram?
- Print out the first fragment of the fragmented IP datagram. What information in
the IP header indicates that the datagram been fragmented? What information in
the IP header indicates whether this is the first fragment versus a latter fragment?
How long is this IP datagram?
- Print out the second fragment of the fragmented IP datagram. What information in
the IP header indicates that this is not the first datagram fragment? Are the more
fragments? How can you tell?
- What fields change in the IP header between the first and second fragment?
Now find the first ICMP Echo Request message that was sent by your computer after you changed the Packet Size in pingplotter to be 3500.
- How many fragments were created from the original datagram?
- What fields change in the IP header among the fragments?
Demonstration and Report
For this assignment you will need to write a report that carefully address each of the following three tasks:
-
Task A (Q1-9):
Based on questions 1-9, please write two paragraphs explaining your observations of the operation
(and implementation) of traceroute, as well as how it leverages the ICMP and IP protocol. You should also
comment on the relationship between these three protocols.
-
Task B (Q10-15):
Based on questions 10-15, please write a paragraph that carefully discusses your observations on fragmentation and how it is implemented.
-
Task C:
Looking at the traceroute results (and/or collecting your own traceroute data), can you observe any impact of packet sizes on the measured round trip times (RTTs)? If possible, please explain and discuss your answer in terms of transmission rates, network distances, number of hops, and other factors that may impact the RTTs. (Recall the discussion on different types of delays.) Your discussion may also benefit from a supporting table!
Note that, similar to previous assignments, you are expected to convince us that you understand the above aspects of traceroute and IP.
Please structure your report such that your answers are clearly
indicated for each question (and section of the assignment).
It is not the TA's task to search for the answers. Both the
questions themselves and the corresponding answers should be
clearly stated (and indicated) in your report. Structure your
report accordingly. Furthermore, your answers should be explained
and supported using additional evidence, when applicable. During
the demonstration the TA may ask similar questions to assess your
understanding of the lab. You are expected to clearly explain and
motivate your answers. As the assignments are done in groups of two,
both members of the group will be asked to answer questions.
Additional instructions and information about the reports can be found
here.
Please take this chance to read the guidelines carefully.